Psychological processes of radicalization
Theoretical Frameworks of Radicalization
The study of radicalization explores the psychological, social, and environmental mechanisms through which individuals transition from mainstream societal norms toward embracing extremist ideologies and, in some instances, committing ideologically motivated violence. Over the past two decades, academic literature has decisively moved away from seeking a monolithic "terrorist profile." Instead, current psychological and sociological paradigms conceptualize radicalization as a dynamic, non-linear developmental process heavily dependent on contextual factors, interpersonal relationships, and cognitive vulnerabilities 12.
To properly investigate this phenomenon, researchers draw a critical analytical distinction between radicalism and extremism. Radicalism is generally understood as a political orientation that operates within democratic boundaries, pushing against liberal norms to pursue fundamental structural change through legal activism. Extremism, conversely, is characterized by a fundamental rejection of democratic principles, pluralism, and the rule of law, coupled with the belief that violence is a legitimate and necessary tool to achieve ideological goals 34.
Cognitive Versus Behavioral Radicalization
The relational nature of these definitions underscores a secondary conceptual tension in the field: the distinction between cognitive radicalization and behavioral radicalization. Cognitive radicalization involves the internalization of increasingly extreme beliefs and the moral justification of violence 4. Behavioral radicalization describes a shift in actions, such as actively participating in an extremist network, organizing logistics, or executing acts of targeted violence 4.
Early counterterrorism models frequently conflated these two dimensions. The most notable example is the "Conveyor Belt" theory, formalized in a 2007 New York Police Department research report, which posited a fixed, sequential trajectory from religious or political conservatism to extremist ideology, inevitably culminating in terrorism 35. Extensive empirical research has subsequently debunked the conveyor belt model. Studies demonstrate that cognitive extremism is neither a strictly reliable predictor nor a universal prerequisite for violent extremism 236. The overwhelming majority of individuals who harbor radical or extremist cognitive beliefs - estimated by some researchers at over 99 percent - never engage in radical action 378. Furthermore, behavioral radicalization can occur independently of deep ideological commitment. Individuals frequently integrate into violent networks for alternative motives, such as financial incentives, thrill-seeking, status elevation, or personal revenge, only adopting the cognitive ideology retroactively to rationalize their actions 789.
The 3N Model of Radicalization
To account for the complex interplay between individual motives and group dynamics, researchers developed the 3N Model of Radicalization. This comprehensive socio-psychological framework identifies three interconnected components necessary for the production of violent extremism: Needs, Narratives, and Networks 1011.
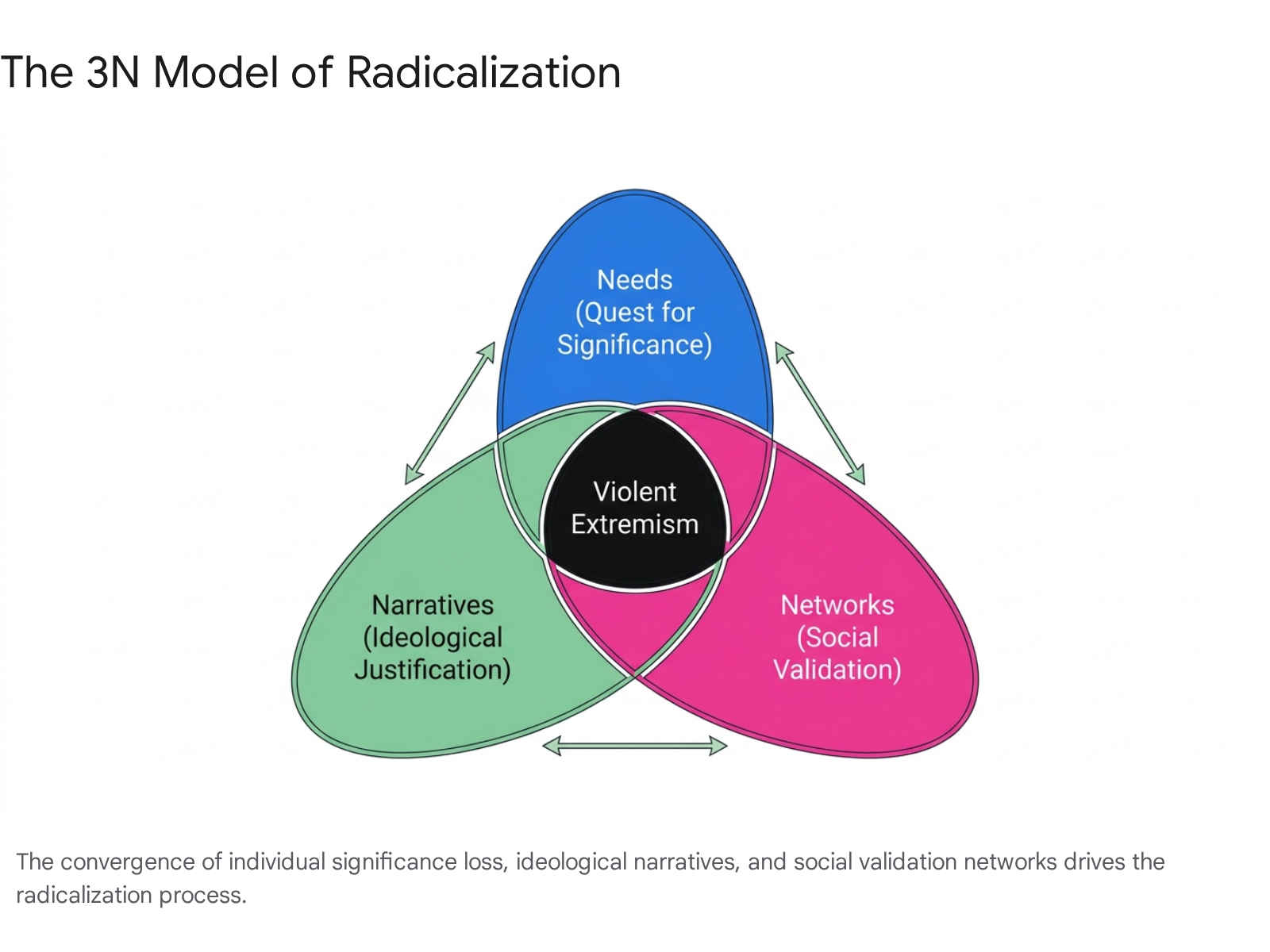
The primary catalyst in the 3N model is the "Need," conceptualized specifically as the "quest for significance." This denotes the fundamental human motivation to matter, to be respected, and to achieve a sense of personal worth 1011. This psychological drive is frequently activated by a profound "loss of significance," which may manifest through personal failures, trauma, humiliation, social alienation, or group-based relative deprivation 110. When individuals feel detached from societal participation or perceive that their broader identity group is unjustly marginalized, they experience a psychological deficit that urgently demands restoration 110.
However, the quest for significance alone does not reliably produce violent extremism; it requires the introduction of a specific ideological "Narrative." Extremist narratives provide a cognitive framework that identifies a specific culprit responsible for the individual's or group's grievances 10. Crucially, these narratives prescribe a method for restoring honor, framing violence against the designated out-group not merely as justifiable, but as a moral imperative. Drawing upon Albert Bandura's theories of moral disengagement, the 3N model argues that extremist narratives allow individuals to bypass normative moral sanctions against murder by dehumanizing targets and portraying violence as a heroic defense of the in-group 10.
The final component is the "Network." The ideological narrative is introduced, validated, and continuously reinforced by a specific social environment. Radical networks reward adherence to the extremist ideology by providing belonging, camaraderie, and bestowed significance 1213. Through psychological mechanisms of identity fusion, the individual deeply internalizes the network's values, blurring the boundaries between personal and group identity. This fusion facilitates extreme self-sacrifice, as the individual begins to perceive the group's survival and success as indistinguishable from their own 14.
Critiques and Limitations of the 3N Model
While the 3N model has achieved a high degree of empirical support across diverse cultural contexts, systematic reviews highlight notable limitations in its predictive application. Meta-analyses indicate significant methodological heterogeneity in how the concept of "significance loss" is operationalized and measured across different studies 15.
Furthermore, some empirical investigations fail to find a direct, unmediated causal link between significance loss and violent extremism. Current research suggests that significance loss only predicts support for political violence when moderated by other psychological variables, such as an obsessive passion for a cause or the pre-existing presence of deviant associations within the individual's social network 1516. These findings indicate that while the 3N framework is highly useful for explaining the retrospective trajectories of known extremists, its utility as a predictive tool for identifying future radicalization in general populations remains debated 15.
Stage and Structural Models of Radicalization
In contrast to the fluid, interacting variables of the 3N model, other researchers utilize structural metaphors to explain the psychological mechanisms that filter broad, aggrieved populations down to a microscopic minority of violent actors. Fathali Moghaddam's "Staircase to Terrorism" metaphor conceptualizes radicalization as an ever-narrowing six-floor building 71718. The ground floor represents massive populations experiencing perceived injustice and relative deprivation. As individuals ascend, they search for solutions (first floor), direct anger at perceived perpetrators (second floor), and undergo moral disengagement to justify terrorism (third floor). By the fourth floor, individuals officially integrate into a radical group, culminating on the fifth floor with the psychological dehumanization of enemy civilians, rendering them legitimate targets for lethal action 1718.
McCauley and Moskalenko's "Two-Pyramids Model" offers a structural adjustment to Moghaddam's framework by explicitly mapping the separation between cognitive and behavioral radicalization 718. The authors argue that treating ideological radicalization and violent action as a single continuum is analytically flawed and frequently leads to counterproductive security policies 18.
| Model Framework | Primary Conceptual Focus | Core Psychological Mechanism | Key Theoretical Contribution |
|---|---|---|---|
| The 3N Model | Motivational forces and social validation networks. | A psychological quest for significance interacting with an ideological narrative. | Rejects linear progression; emphasizes the simultaneous convergence of distinct sociopsychological forces. |
| Staircase to Terrorism | Sequential psychological stages of behavioral escalation. | The progressive accumulation of unresolved grievances, displaced anger, and moral disengagement. | Illustrates how massive populations at the base filter down to a tiny fraction of violent actors at the apex. |
| Two-Pyramids Model | The structural separation of radical beliefs from radical actions. | Identifies independent escalation tracks for ideological opinions versus physical behaviors. | Explains why the vast majority of ideological radicals remain non-violent, and why non-ideologues commit violence. |
Ideological Variations in Radicalization Pathways
Radicalization pathways are fundamentally shaped by the specific ideological milieu an individual encounters. While the underlying psychological drivers - such as significance loss, perceived humiliation, or identity fusion - demonstrate remarkable consistency across movements, the specific narratives and recruitment vectors diverge significantly 141920.
Religious Extremism and Salafi-Jihadism
The psychology of Islamist radicalization relies heavily on the mobilization of collective relative deprivation and global grievance narratives. Violent extremist organizations (VEOs) such as Al-Qaeda and the Islamic State (ISIS) construct narratives that frame highly localized political conflicts and broader geopolitical events as evidence of a systemic, existential war against Islam 914. This provides recruits with a transcendent, culturally unifying identity that supersedes local or tribal affiliations.
Radicalization within this context frequently involves a "cognitive opening" - a period of acute psychological vulnerability following a personal crisis, social exclusion, or community trauma . During this opening, individuals become highly receptive to fundamentalist reinterpretations of religious doctrine. The extremist narrative emphasizes that participation in violent jihad is not merely a political tactic, but an immediate, divine mandate that restores both individual honor and the global Muslim community's dignity, thereby perfectly fulfilling the individual's quest for significance 914.
Far-Right and Anti-Government Extremism
Far-right and white supremacist radicalization is typically anchored in narratives of racial hierarchy, anti-government paranoia, and civilizational decline. A dominant psychological driver in this milieu is the "Great Replacement" conspiracy theory, which stokes existential dread by positing that white populations in Western nations are being systematically replaced by non-white immigrants through the orchestrations of shadowy elites 2021.
Unlike the highly structured, group-centric nature of traditional jihadist networks, contemporary far-right extremism increasingly manifests through "post-organizational" dynamics 2223. Radicalization occurs not in physical training camps or formal organizations, but within decentralized, transnational digital subcultures. Individuals operating as lone actors often lack formal affiliations with established hate groups, yet they absorb rigid tactical scripts, moral justifications, and ideological inspiration from online manifestos and the digital veneration of previous mass shooters 2223.
Incel and Manosphere Extremism
The "manosphere" refers to an overlapping network of anti-feminist online communities, the most radical of which is the involuntary celibate (incel) subculture. Incel radicalization represents a highly specific psychological pathway rooted in biological determinism, perceived sexual marginalization, and profound fatalism 2425. The subculture utilizes an insular, highly specific lexicon to socialize members through increasingly extreme ideological "pills." This process culminates in the adoption of the "blackpill" ideology - a deeply nihilistic worldview asserting that societal hierarchies are based entirely on immutable physical attractiveness, permanently subjugating those deemed genetically inferior 25.
Recent empirical research proposes a "dual pathways hypothesis" to explain the progression toward incel-related violence. The first pathway is driven by experiential vulnerabilities, such as a documented history of adolescent bullying, autism spectrum traits, and low self-perceived mate value 26. The second pathway is driven by dispositional characteristics, including Dark Triad personality traits (narcissism, Machiavellianism, psychopathy) and generalized right-wing political orientations 26. Because incel extremism is deeply intertwined with perceived immutable physical characteristics and severe mental health challenges - rather than purely theological or political grievances - traditional cognitive deradicalization strategies based on narrative debate face extreme difficulties in this milieu 24.
Digital Ecosystems and Online Radicalization
The architecture of the modern internet has fundamentally altered both the pace and the mechanics of the radicalization process. A psychological transition that historically unfolded over months or years of physical, face-to-face indoctrination can now occur in a matter of days or weeks through immersive digital ecosystems 2728.
Algorithmic Amplification on Mainstream Platforms
Mainstream social media platforms utilizing sophisticated algorithmic recommendation systems (e.g., TikTok, YouTube, X) increasingly serve as low-threshold gateways into extremist ecosystems 2729. Algorithms designed to maximize user engagement and retention frequently promote emotionally charged, polarizing, or outrage-inducing content.
This dynamic was highly visible following the October 2023 Hamas attack on Israel, where European security investigators documented a rapid surge in algorithmic radicalization among adolescents. Emotionally vulnerable, digitally native youths were rapidly exposed to algorithmically curated "victimhood-revenge" narratives and Salafi-jihadist propaganda via short-form video platforms. In several documented cases in Europe, this digital exposure rapidly accelerated youths' transition from passive content consumers to individuals actively plotting domestic terror attacks, highlighting the potent intersection of youth online culture and algorithmic influence 29.
The Decentralized Web and Encrypted Networks
As mainstream platforms implement stricter content moderation policies to combat Terrorist and Violent Extremist Content (TVEC), researchers observe a consistent "displacement effect." Extremist actors adapt by migrating their operations to the decentralized web (DWeb) and encrypted messaging applications 3031. Platforms such as Telegram, Signal, Odysee, and Fediverse-based applications (e.g., PeerTube) offer digital safe havens characterized by minimal moderation, high user anonymity, and resistance to platform-level takedowns 2232.
Within these decentralized enclaves, radicalization functions through highly concentrated echo chambers. The communication logic of terrorism has shifted; rather than executing attacks to attract traditional media coverage, extremists engage in "direct-to-audience" performance. Lone actors livestream attacks and distribute manifestos directly to imageboards and encrypted channels, generating a self-reinforcing digital subculture that provides immediate ideological framing, recognition, and social validation to geographically isolated individuals 22.
Gaming Platforms and Adjacent Ecosystems
Extremist networks are increasingly exploiting online gaming platforms (e.g., Roblox) and adjacent communication servers (e.g., Discord) to target younger demographics 2728. Radicalization in these spaces diverges from traditional propaganda distribution, operating instead through cultural appropriation. Extremists utilize in-game lore, character archetypes, user-generated modding, and meme formats to normalize far-right ideologies and violence within the context of gameplay 2833.
Because these interactions blend seamlessly with leisure and entertainment, they lower the cognitive defenses of participants. This functions as a form of distributed indoctrination, where users are radicalized through sustained, gamified exposure to extremist symbolism and role-playing scenarios rather than explicit political recruitment 428.
Regional Dynamics in Non-Western Contexts
While Western academic literature frequently emphasizes domestic lone-actor extremism or global jihadism threatening the Global North, radicalization pathways exhibit significant variation in non-Western contexts. In these regions, radicalization is uniquely driven by local structural grievances, severe socioeconomic pressures, and geopolitical instability 2734.
Central Asia and Labor Migration
In Central Asia - particularly within Tajikistan, Uzbekistan, and Kyrgyzstan - radicalization pathways are heavily influenced by state repression of political Islam, historical border disputes in the Fergana Valley, and the economic necessity of massive labor migration 3536. The Islamic State in Khorasan Province (ISKP) has successfully exploited these systemic vulnerabilities, aggressively expanding its recruitment of Central Asian nationals. United Nations estimates suggest that ISKP fighters and associated family members from Central Asia number between 4,000 and 6,000 individuals 37.
Crucially, radicalization frequently occurs not within the individuals' home countries, but among marginalized Central Asian diaspora and labor migrant populations residing in Russia or Europe. In these environments, individuals experience severe social alienation, economic hardship, and discrimination, creating fertile psychological ground for ISKP's digital recruitment efforts 37. The persistent threat posed by this dynamic was demonstrated by the March 2024 ISKP attack on the Crocus City Hall in Moscow, as well as numerous disrupted plots targeting European infrastructure 37.
Southeast Asia
The radicalization landscape in Southeast Asia (notably Indonesia, Malaysia, and the Philippines) has undergone a significant transition from entrenched militant organizations to decentralized, online-inspired lone actors 33. The historical evolution and eventual dissolution of major groups like Jemaah Islamiyah (JI) demonstrates that deeply entrenched organizations can undergo profound ideological re-evaluation; JI's shift away from violent jihadism was largely driven by internal theological reflection and expert reasoning (ijtihad), proving that Islamic hermeneutics can dismantle extremist ideologies from within 38.
However, the operational vacuum left by the decline of structured groups has been filled by pro-ISIS cyber-based strategies 33. Southeast Asian authorities face complex challenges in distinguishing between individuals merely consuming online extremist rhetoric and those actively mobilizing for violence. Current data indicates that digital radicalization in the region rarely occurs in total isolation; online propaganda consumption frequently serves to reinforce pre-existing offline trust networks and family ties 38. Furthermore, rising Hindu nationalism in India and the emergence of neo-fascist online groups in the Philippines demonstrate that youth radicalization in the region is diversifying well beyond Islamic fundamentalism 27.
Sub-Saharan Africa
In sub-Saharan Africa, radicalization pathways are deeply intertwined with poverty, high youth unemployment, and the unintended consequences of state security operations. In Kenya, the recruitment dynamics of the militant group Al-Shabaab reveal stark deviations from purely ideological models of radicalization. Fieldwork indicates that approximately half of radicalized individuals join the group primarily for economic reasons; in areas suffering from up to 90 percent youth unemployment, Al-Shabaab recruiters promise monthly salaries that vastly exceed the national average 9.
However, this economic pull is heavily compounded by systemic sociopolitical grievances. Many Muslim youths in Kenya join extremist groups as a direct counter-reaction to perceived collective punishment, systemic marginalization, and ethnic profiling by state security forces 39. Additionally, qualitative research in Mandera County challenges the traditional framing of women exclusively as passive victims of radicalization. Evidence shows that Kenyan Muslim women actively exercise agency, making rational choices to participate in both combatant and vital non-combatant logistical roles within Al-Shabaab's operational networks 40.
Disengagement and Countering Violent Extremism
Understanding the psychological mechanisms through which individuals exit violent extremist groups is as critical for public safety as understanding how they enter. Within the fields of criminology and terrorism studies, practitioners draw a strict conceptual distinction between the processes of deradicalization and disengagement 4142.
Deradicalization is defined as a deep cognitive process involving the total rejection of the extremist belief system and the embracing of mainstream societal values 41. Disengagement, conversely, is a strictly behavioral process denoting the cessation of violent activity and physical separation from the extremist group. Crucially, behavioral disengagement frequently occurs while the individual still harbors radical ideological beliefs 414243.
Push and Pull Factors in Disengagement
Psychologist John Horgan's foundational research utilizes a "push-pull" framework to categorize the complex catalysts for terrorist disengagement 4244. Push factors represent negative forces internal to the extremist experience that drive an individual away from the group. Pull factors represent positive external forces that attract the individual back toward conventional society 4445.
Quantitative analyses of autobiographical defector accounts indicate that push factors - particularly disillusionment with group strategy and conflict with personnel - are cited much more frequently as the primary catalyst for leaving than formal ideological deradicalization 4345. Consequently, interventions focused on exploiting "role strain" and exposing organizational hypocrisy are often more effective for initiating immediate behavioral disengagement than attempts to debate theological or political doctrine 43.
| Factor Category | Specific Mechanisms and Examples | Psychological Impact on the Individual |
|---|---|---|
| Push Factors (Internal to the Group) | Disillusionment with leaders; Burnout; Disgust with excessive violence against civilians; Tactical disagreements; Hypocrisy in resource distribution. | Generates severe cognitive dissonance and role strain, eroding the psychological benefits (significance and belonging) the group initially provided. |
| Pull Factors (External to the Group) | The desire to marry or start a family; New educational or employment demands; Positive interpersonal interactions with out-group moderates; Offers of state amnesty. | Offers alternative, legitimate, and less dangerous avenues for fulfilling the quest for personal significance and community integration. |
Digital Interventions and the Redirect Method
To interrupt the radicalization process before individuals fully integrate into violent networks, technology companies and civil society organizations employ targeted online interventions. A prominent example is the "Redirect Method," a methodology developed by Jigsaw (Google) in partnership with the social enterprise Moonshot CVE 464748.
Instead of relying on broad, untargeted public messaging campaigns, the Redirect Method utilizes advertising technology to intercept user "intent signals." When vulnerable individuals query search engines using specific high-risk keywords - such as white supremacist slogans, incel jargon, or jihadist propaganda terms - the algorithm serves them targeted advertisements leading to curated, alternative viewpoints 4849. These counternarratives are typically generated by credible, organic voices within the community, such as defectors ("formers"), religious scholars, or mental health professionals, significantly increasing their authenticity compared to formal government messaging 47. The underlying philosophy of this approach posits that an online search for extremist material represents both a high risk of potential harm and a brief window of "cognitive opening" where digital interventions can effectively challenge dangerous beliefs 49.
Methodological Challenges in Evaluating Interventions
Despite the proliferation of online Countering Violent Extremism (CVE) campaigns, accurately evaluating their real-world impact remains exceptionally difficult due to profound methodological and ethical limitations 485051.
Currently, the evaluation of online interventions relies heavily on "vanity metrics" or reach data (e.g., ad impressions, click-through rates, video views) provided by the technology platforms hosting the campaigns. While these metrics indicate that counter-narrative content was successfully delivered and consumed, they offer zero diagnostic insight into whether the intervention actually shifted the target audience's cognitive attitudes or prevented behavioral violence 4851.
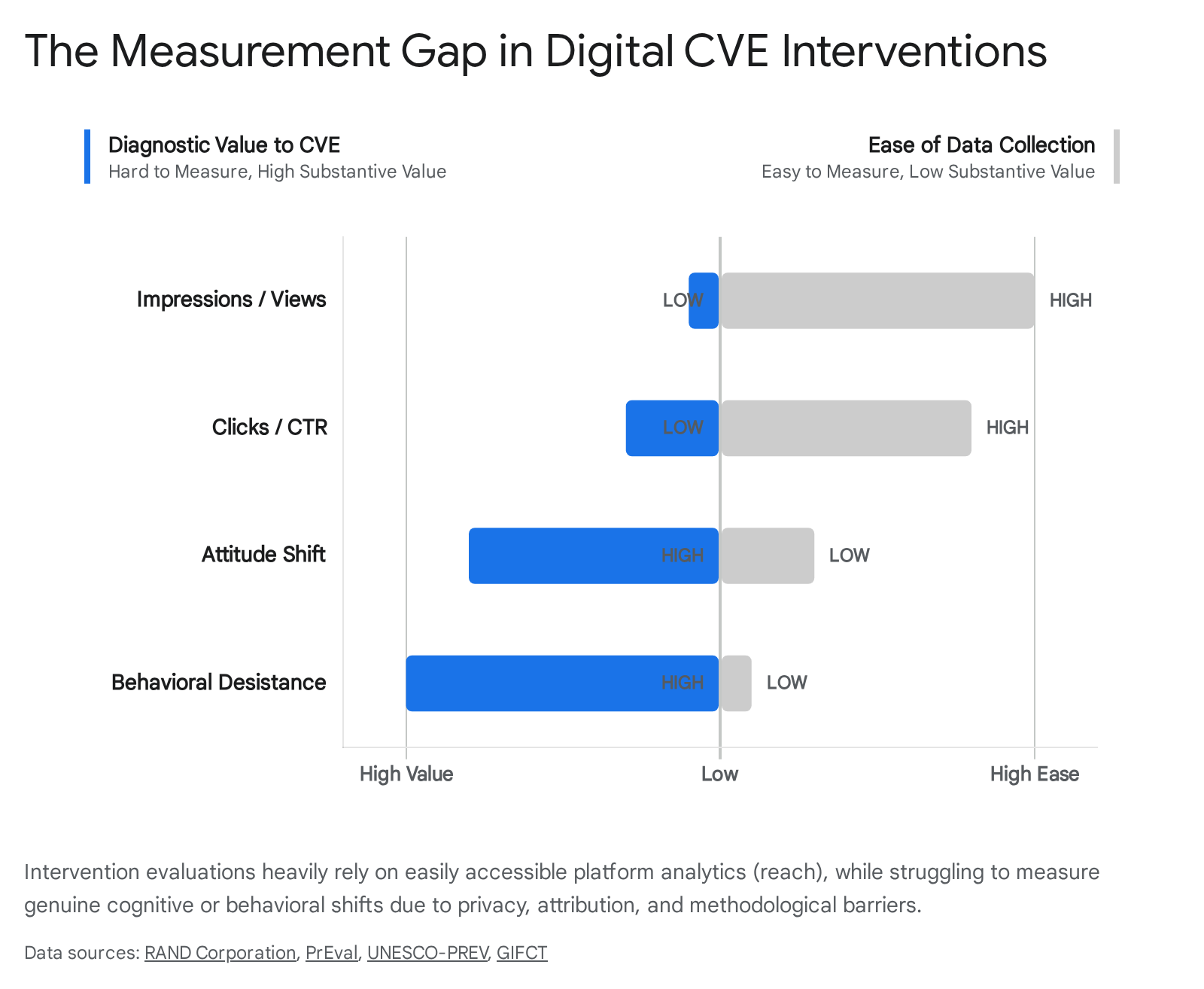
Attributing real-world behavioral changes to a specific digital intervention is scientifically problematic. Researchers lack access to the granular, cross-platform private data held by technology corporations, forcing a reliance on incomplete open-source intelligence 5253. Furthermore, establishing rigorous experimental control groups for online interventions violates ethical standards regarding the deliberate, unmitigated exposure of individuals to extremist content. Finally, tracking users longitudinally relies on self-selection, and the high degree of anonymity afforded by modern digital networks makes tracking an individual's trajectory from online query to offline desistance virtually impossible without severely compromising civil liberties and data privacy laws 5054.
Conclusion
The psychology of radicalization cannot be reduced to a specific demographic profile or a rigid, teleological progression from conservative thought to violent action. Rather, it represents a highly volatile intersection of individual cognitive vulnerabilities, socially validating peer networks, and specific ideological narratives that weaponize human grievances. As decentralized digital ecosystems, gaming platforms, and algorithmic amplification continue to accelerate the spread of hybridized, post-organizational extremism, traditional counterterrorism models focused solely on theological debate must adapt. Effective prevention and disengagement strategies require dismantling the social utility of extremist networks, exploiting organizational role strain, and offering vulnerable individuals legitimate, structural pathways to restore their sense of personal and collective significance.