Mechanics of product virality and referral growth
The mechanics of product virality and referral growth represent a complex intersection of mathematical modeling, behavioral economics, algorithmic network topologies, and advanced data architecture. In contemporary digital ecosystems, organic growth is rarely the result of serendipity; it is engineered through systematic frameworks that incentivize user-to-user sharing. This report synthesizes current research on viral distribution, examining the mathematical models that quantify virality, the structural shift from traditional acquisition funnels to integrated growth loops, the psychological drivers underpinning gamified social commerce, and the technological landscape that dictates how referral data is tracked in a privacy-restricted environment.
Foundational Mathematics of Viral Distribution
The study of viral distribution in digital products is deeply rooted in epidemiological modeling and quantitative network analysis. To understand how a product grows organically, researchers and practitioners utilize mathematical frameworks that measure the rate, velocity, and sustainability of sharing behaviors.
The K-Factor and Viral Coefficient Dynamics
The canonical metric for evaluating viral growth is the K-factor, frequently referred to interchangeably as the viral coefficient. The K-factor is a quantitative measure representing the average number of new users that each existing user successfully converts and brings onto a platform 12. The mathematical formulation is generally expressed as $K = i \times c$, where $i$ represents the number of invitations or sharing actions initiated by an existing user, and $c$ represents the conversion rate of those invitations into fully activated new users 122.
The value of the K-factor dictates the baseline growth trajectory of the user base without external paid acquisition: * Sublinear Growth ($K < 1$): Existing users bring in new users, but the replacement rate is insufficient for self-sustaining growth. The viral loop will eventually decay and plateau without external marketing input 22. * Linear Growth ($K = 1$): Each user perfectly replaces themselves with one new user, maintaining a steady state 2. * Exponential Growth ($K > 1$): Each user brings in more than one new user, triggering compounding, self-sustaining expansion 122.
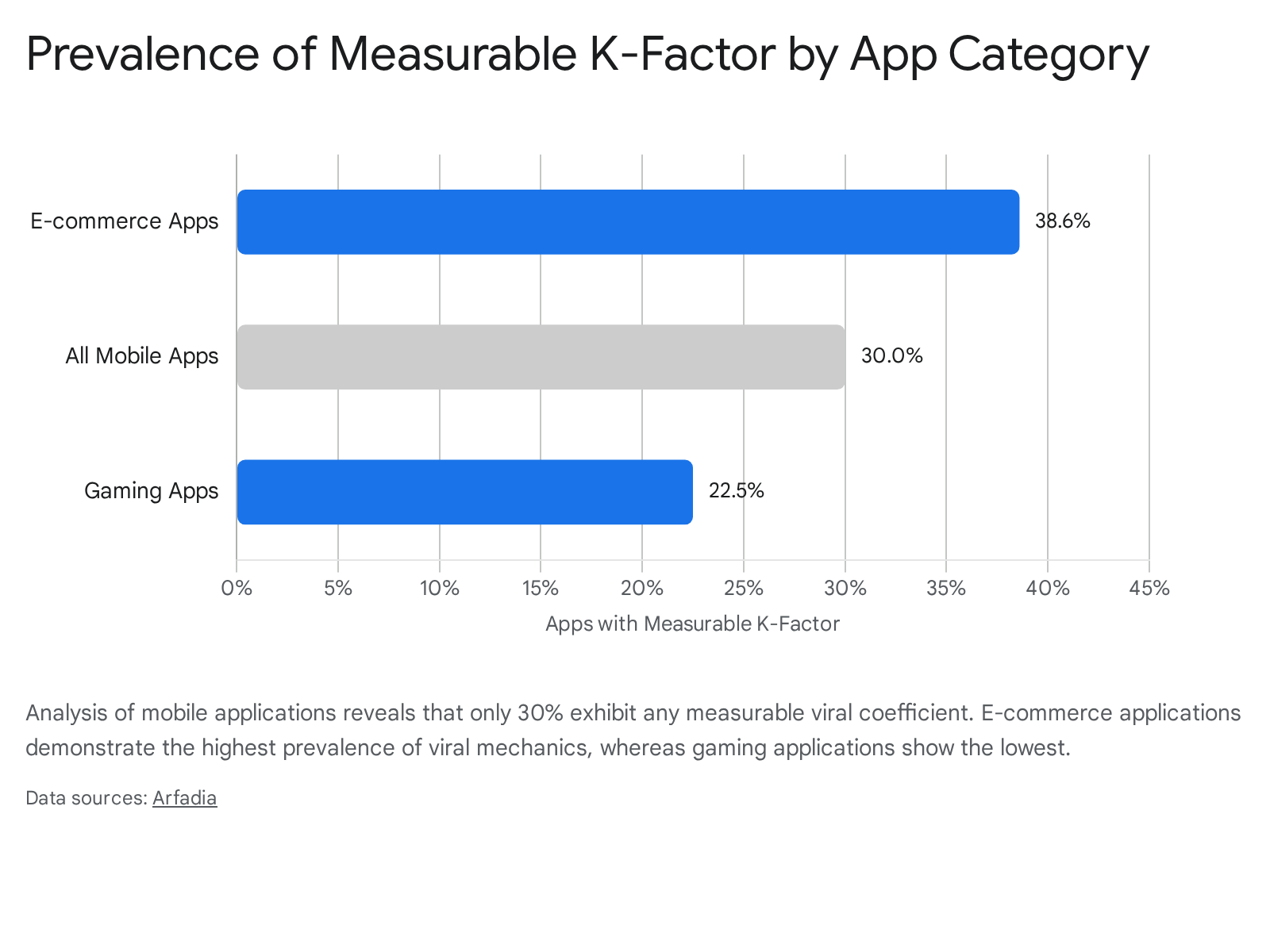
While achieving a K-factor greater than 1.0 is a theoretical ideal, industry benchmarks indicate that it is an exceptionally rare achievement, with fewer than 0.001% of consumer internet companies sustaining it structurally over extended periods 1. Recent empirical research examining thousands of digital products suggests that a K-factor between 0.15 and 0.25 is generally considered a strong baseline that significantly reduces blended customer acquisition costs, a coefficient of 0.40 is considered highly effective, and any coefficient exceeding 0.70 represents elite viral mechanics 1.
Equally critical to the viral coefficient is the Viral Cycle Time ($ct$), defined as the duration required to complete one full invitation-to-conversion cycle 24. The mathematics of exponential growth demonstrate that overall user acquisition is exponentially influenced by shorter cycle times. Reducing the end-to-end viral cycle from two days to one day can alter the resultant user base magnitude from tens of thousands to tens of millions by the twentieth viral cycle, demonstrating that velocity is an equally weighted variable alongside raw conversion rates 12. Consumer applications typically target viral cycles of one to three days, while business-to-business (B2B) products experience longer cycles spanning one to eight weeks 1.
Epidemic Modeling in Digital Networks
Academic researchers frequently model digital virality using frameworks derived from epidemiological studies, treating digital referrals and product adoption similarly to infectious diseases 34. Fractional-order computer virus propagation models, such as the SIS (Susceptible-Infected-Susceptible) model, utilize a basic reproduction number ($R_0$) to determine whether an information cascade will survive or become extinct within a given topology 356.
In these epidemiological models, if $R_0 < 1$, the digital phenomenon gradually disappears; if $R_0 > 1$, the phenomenon continues to spread until it hits a herd immunity or market saturation threshold, defined mathematically as $s_c = 1/R_0$ 36. Furthermore, research highlights that network heterogeneity severely affects transmission. In scale-free networks, high initial "viral loads" (the frequency or intensity of the initial marketing push or early user seed) increase infection prevalence 6. However, the presence of low-degree nodes - users with small or inactive social networks - acts as "transmission dead ends," degrading the viral coefficient rapidly and limiting broad dissemination 6.
The structural model of the network dictates the propagation limits. Studies of information diffusion demonstrate that while most memes and viral content spread like complex contagions requiring social reinforcement and homophily, true systemic virality is predicted by a meme's early spreading pattern across multiple distinct community structures 78. The more disparate communities a piece of content or a product referral penetrates early in its lifecycle, the higher its ultimate peak popularity 7.
Emergent Viral Measurement Metrics
As the digital landscape fragments across multiple platforms, traditional single-platform K-factor calculations are frequently augmented by more sophisticated metrics to capture nuanced sharing behaviors 1. Systematic reviews of contemporary viral marketing indicate an industry shift toward composite analytics 19.
New metrics utilized in advanced product growth models include: * Viral Velocity Index (VVI): A metric that quantifies the speed at which content is shared and reshared within a specific time window, prioritizing immediate acceleration vectors over long-term cumulative volume 1. * Community Amplification Score (CAS): A measure of genuine, organic community-driven growth that isolates and filters out automated bot activity or financially incentivized sharing to determine the intrinsic network effect value 1. * Cross-Platform Viral Coefficient (CPVC): An emerging framework designed to track convoluted user journeys across fragmented environments, accommodating scenarios where an invitation might be distributed via WhatsApp, viewed on Twitter, and converted on a mobile application store 1.
The Structural Shift to Self-Reinforcing Growth Loops
Historically, digital marketing and product growth relied heavily on the concept of the "funnel" - a linear pathway where prospects are acquired at the top through paid media channels, activated in the middle, and eventually monetized at the bottom 1213.
Limitations of Traditional Acquisition Funnels
Modern product research indicates that linear funnels create organizational silos, encourage one-off acquisition thinking, and suffer from rapidly diminishing returns 1213. As digital advertising environments become more competitive, funnels require continuous capital injection to maintain top-of-funnel flow. When paid acquisition ceases, growth halts entirely, exposing the business to escalating Customer Acquisition Costs (CAC) 1213.
Archetypes of Product Growth Loops
To engineer sustainable product virality, contemporary architecture relies on integrated "growth loops." A growth loop is defined as a closed, self-reinforcing system where the inputs of one cycle (e.g., the actions of a new user) directly generate the outputs necessary for the next cycle (e.g., the acquisition of subsequent new users), systematically reducing CAC as momentum builds 121011.
| Growth Loop Archetype | Mechanism of Action | Industry Example |
|---|---|---|
| Personal Viral Loops | Value increases for the inviter only when their specific network joins. | Communication applications (WhatsApp) requiring mutual adoption for utility 10. |
| Usage-Based Loops | Core product functionality naturally exposes non-users during normal operation. | Screen recording tools (Loom) auto-playing for recipients who must sign up 12. |
| Referral Loops | Explicit financial or feature-based incentives offered to existing users to invite peers. | Cloud storage (Dropbox) offering double-sided storage space rewards 112. |
| Collaboration Loops | Shared workspaces inherently require new users to join to participate in tasks. | Enterprise productivity platforms requiring team invites for project access 12. |
| User-Generated Content (UGC) | User contributions fuel external search engine discovery, attracting new users. | Public forums and content platforms where indexed user posts drive inbound traffic 12. |
The Reforge Framework and Capital Accumulation
The effectiveness of any growth loop is contingent upon the underlying incentives driving the user to complete the action. Behavioral frameworks emphasize that users participate in viral loops to accrue three primary forms of capital: personal, financial, and social 10.
Personal viral loops occur when the product's fundamental utility improves for the inviter as more of their immediate network joins. In these models, the value distributor is the user themselves. This creates a highly defensible network effect; the value promise is unique to the user's specific social graph, making replication by competing platforms exceedingly difficult and structurally locking in the user base 10.
Behavioral Economics and Gamified Social Commerce
The practical application of viral loops and behavioral economics is most evident in the Asian social commerce sector. The ecosystem is dominated by super-apps that seamlessly blend e-commerce transactions, social networking, and interactive gaming. The rapid market penetration of platforms like Pinduoduo provides a comprehensive empirical case study in engineered product virality and gamified referral mechanics 12.
The Group Purchasing Architecture
Pinduoduo utilized a business model heavily reliant on consumer-to-manufacturer (C2M) interactions and a viral group-buying feature known as Tuangou (Team Purchasing) 171314. The architecture of Tuangou requires users to form a collective team - typically within a strict 24-hour window - to unlock a heavily discounted acquisition price 1720.
Unlike traditional e-commerce platforms such as Alibaba and JD.com, which optimize purely for funnel conversion, cart checkouts, and transactional efficiency, the team purchasing model mimics the offline communal shopping experience 1220. This approach capitalizes on collectivist cultural mindsets, which are particularly prevalent in lower-tier Chinese cities where purchasing decisions are frequently made within tight familial or community networks 1220.
By offering two distinct prices - a standard price for individual purchases and a drastically reduced price for team purchases - the platform relies on the behavioral principle of "pricing on purpose." The disparity between the prices creates an irresistible value proposition, effectively compelling users to act as unpaid acquisition agents for the platform 14. The initiator receives the material benefit of a price reduction, while the invited participant receives the same discount alongside the social reward of the initiator's gratitude. This dynamic strengthens social bonds through mutual advantage, building consumer trust through established social circles rather than corporate branding 12.
Intrinsic Motivation and Game Mechanics
Social commerce platforms augment team purchasing with sophisticated gamification mechanics designed to drive daily active user (DAU) retention, habitual engagement, and continuous viral sharing 131516. Features such as "Price Chop" allow users to obtain products entirely for free, provided they can rally a sufficient number of peers to click their shared referral links within a specific time limit 1420. As the price approaches zero, each incremental click grants a progressively smaller discount, requiring the user to invite exponentially more people to finalize the transaction. This mechanism leverages the behavioral economics principle of loss aversion; users who have already invested significant social capital in lowering the price will aggressively recruit more users to avoid losing their progress 2015.
Additionally, internal mechanics like "Duo Duo Orchard" allow users to cultivate virtual trees by logging in daily, inviting friends, and making purchases. This prolonged engagement loop eventually results in real, physical agricultural products being shipped to the user's home 20. While not inherently multiplayer, these features incorporate social cooperation elements, allowing users to interact with peers' virtual assets, further embedding the product into their daily social routines 1420.
Quantitative Impacts of Gamification on Engagement
Quantitative studies assessing gamification in e-commerce demonstrate substantial behavioral shifts. Analysis of 15,000 users interacting with gamified platforms over six months revealed that features relying on positive reinforcement and leaderboard social comparisons significantly increase core metrics 15.
Users engaging with these gamified loops demonstrated average session lengths of 18.4 minutes, a purchase frequency of 4.2 transactions within the period, and a 67% reward redemption rate 15. Furthermore, strong positive correlations were observed between session length, leaderboard interaction, and overall referral rates ($r = 0.52$) 15. These findings indicate that intrinsic game mechanics act as a powerful catalyst for extrinsic economic behaviors, leveraging psychological stimuli such as social proof and positive reinforcement to artificially inflate the $i$ (invitation) variable in the viral coefficient equation 1517.
Network Topologies and the Interest Graph
While traditional referral programs and gamified loops relied heavily on existing interpersonal connections, the architecture of digital virality is undergoing a fundamental structural paradigm shift. The primary mechanism for information distribution is rapidly moving away from the "Social Graph" toward the "Interest Graph."
Transition from Social Connections to Behavioral Signals
For over a decade, digital visibility and virality were functions of relation. The Social Graph distributed content based on an individual's explicit connections, friend networks, and established social capital 18. In this historical model, virality was inherently constrained by the size of the initial seed audience; entities with massive follower counts enjoyed asymmetric distribution advantages 1819.
The Interest Graph, conversely, operates as a continuous adaptation machine that distributes content based on inferred relevance, behavioral signals, and algorithmic matching, strictly regardless of explicit user connections 181920. Within an interest-driven ecosystem, visibility is not accumulated linearly through follower counts; it is renegotiated moment by moment based on the immediate performance of the content 1821.
| Architectural Feature | The Social Graph Model | The Interest Graph Model |
|---|---|---|
| Core Distribution Mechanism | Relational (Followers, Friends, Connections) | Behavioral (Engagement, Dwell time, Re-watches) |
| Audience Structure | Static and accumulated progressively over time | Fluid, temporary, and highly context-dependent |
| Prerequisite for Virality | Large existing network or established influencer status | High content relevance and immediate engagement signals |
| Measurement Focus | Follower growth rate, Network breadth | Watch completion rate, Comment density, Algorithmic velocity |
This transition establishes a pure meritocracy of content, democratizing viral potential. It destabilizes accumulated social capital, allowing entities with zero preexisting followers to achieve massive exponential reach if their output aligns tightly with real-time audience behaviors 12122.
Algorithmic Virality and Recommendation Engines
The most prominent manifestation of the Interest Graph is TikTok's recommendation engine, colloquially known as the "For You Page" (FYP). Academic and technical research indicates that the FYP is a real-time recommendation engine that explicitly prioritizes content consumption over social connections 23. By analyzing initial interactions - specifically prioritizing deep engagement metrics like video completion rates and re-watches over explicit "likes" - the algorithm bypasses the need for established follower networks 2324.
The underlying machine learning architecture utilizes high-dimensional user and item embeddings, allowing the system to achieve hyper-personalization and predict core content preferences within 60 minutes of a new user's activity 23. To solve the "cold start" problem for new content or new users, the system utilizes bootstrapping: introducing videos to a small, diverse sample of users to gather initial performance metrics. If these initial signals are strong, the system scales distribution instantly 23. To prevent audience stagnation, the recommendation engine employs multi-objective optimization, explicitly calculating diversity scores as a regularization term to manage the exploration-exploitation trade-off 23. Executing this complex matching requires highly optimized inference servers and distributed caching systems capable of retrieving vectors with sub-100 millisecond latency 23.
Clustered Publics and Siloed Virality
Recent academic research by Lee and Umback (2025/2026) conceptualizes the socio-cultural impact of the Interest Graph through the creation of "clustered publics" - algorithmically defined groups of users who receive related material regardless of their social proximity 2425. In this structural model, virality is entirely contingent upon the intensity of engagement signals within specific subcultural silos rather than broad, mass-market network dissemination 2425.
This "siloed virality" means that a product or piece of content does not need to appeal to the general population to achieve a high K-factor. It only needs to resonate deeply within an algorithmically identified niche to trigger exponential algorithmic promotion 2526. However, longitudinal time-series analyses of viral events using Bayesian structural models indicate that algorithmically driven virality is often highly transient. While unexpected news or content can reactivate a collective response process causing a sudden spike in visibility, these quick viral effects fade rapidly 2728. Viral events frequently reverse prior engagement trends but rarely lead to sustained, persistent growth without consistent, steady attention-building strategies to anchor the newly acquired user base 2728.
Psychological Friction and Digital Fatigue
Despite the mathematical efficiency of growth loops and the distribution power of Interest Graphs, the sustainability of product virality is increasingly threatened by fundamental human psychological limits. The proliferation of gamified referral mechanics, persistent notifications, and hyper-optimized algorithmic feeds has led to a measurable phenomenon known as digital fatigue.
Cognitive Overload in the Attention Economy
Digital fatigue is formally defined as a state of cognitive and emotional exhaustion resulting from excessive exposure to digital stimuli and continuous engagement with information technologies 2930. In the contemporary attention economy, the perpetual connectivity demanded by social platforms overwhelms users' finite attentional resources 2931.
Psychological research employing Cognitive Load Theory and Bounded Rationality Theory indicates that when consumers reach cognitive saturation through digital fatigue, their ability to critically evaluate information declines 29. This leads to decision paralysis, diminished satisfaction, and a decreased motivation to engage with digital content - including referral prompts and viral loops 29. The "Online Fatigue Scale," developed specifically to assess this phenomenon, identifies two primary subscales: Off-Balance Fatigue and Virtual Relations Fatigue. High scores on these scales correlate directly with psychosomatic symptoms, emotional exhaustion, and poorer psychological well-being 32.
Consumer Resistance Behaviors
As a direct consequence of this cognitive overload, users are actively developing resistance behaviors against algorithmic personalization and engineered viral marketing. Phenomenological studies investigating urban consumers reveal that 84% of participants experience mental fatigue directly attributed to algorithm-driven content repetition and intrusive notifications 33.
Crucially, consumer resistance is not merely passive avoidance; it is an active renegotiation of digital agency. Consumers deploy strategies ranging from browsing in incognito modes and frequently clearing cookies, to intentionally clicking unrelated content in an attempt to confuse and manipulate recommendation systems 33. Older demographic segments frequently favor withdrawal methods, such as abruptly uninstalling applications to escape decision overload 33. For product growth models heavily reliant on sustained viral coefficients, this widespread consumer distrust and emotional exhaustion represents a critical friction point. It fundamentally degrades the $c$ (conversion rate) variable in the K-factor equation, demonstrating that algorithms must account for emotional thresholds, not just interaction metrics 233.
Technical Degradation of Referral Attribution
Beyond the psychological friction introduced by digital fatigue, the mechanics of referral growth and performance marketing are currently facing severe technical degradation due to aggressive privacy interventions by major operating systems and web browsers.
Apple Link Tracking Protection and Browser Restrictions
Apple's progressive tightening of digital privacy infrastructure has fundamentally disrupted traditional referral attribution models. Building upon previous iterations of Intelligent Tracking Prevention (ITP) and App Tracking Transparency (ATT), Apple introduced Link Tracking Protection (LTP) with iOS 17, expanding it significantly in iOS 18 and iOS 26 404142.
LTP is engineered to thwart cross-site conversion tracking. It automatically strips user-identifiable tracking query parameters (click IDs) from URLs when links are clicked within Apple Mail, Messages, or Safari's Private Browsing mode 414344. Identifiers utilized by major ad networks and affiliate programs - such as Google's gclid, Meta's fbclid, and specific affiliate platform click IDs - are aggressively stripped before the user's browser ever reaches the destination website 414234. While holistic campaign UTM parameters (e.g., utm_source or utm_medium) generally remain intact because they track broader aggregate campaigns rather than individual users, the loss of granular click IDs destroys deterministic user-level attribution 414647.
Furthermore, Safari 26 introduced Advanced Fingerprinting Protection (AFP), which restricts client-side scripts from accessing high-entropy device APIs (such as canvas or audio data) and severely limits long-term browser storage capabilities 3435. This prevents tracking networks from creating persistent probabilistic IDs, making it nearly impossible to connect an initial viral referral click with a delayed product conversion that occurs days later 3436.
Impacts on Campaign Measurement and Return on Investment
For growth marketers and product managers, these technical restrictions create severe attribution gaps 4037. A referral link shared organically between users in an iMessage thread will be stripped of its vital tracking parameters. When the recipient subsequently downloads the app or purchases the product, the conversion cannot be traced back to the specific referring user. This breaks the mathematical measurement of the viral loop 404437.
Industry reports indicate that ad blockers and browser-level privacy defaults are currently obscuring up to 40% of referral traffic in key markets 37. Without accurate visibility into which users and specific distribution channels are driving the highest K-factors, optimizing product virality becomes a matter of guesswork. This leads to inefficient capital allocation, an inability to accurately calculate Return on Ad Spend (ROAS), and prevents platforms from correctly identifying and rewarding successful referrers 373852. Conversely, implementing rigorous anti-fraud solutions remains necessary to combat malicious practices like "cookie stuffing," where fraudulent affiliates exploit attribution windows to claim illegitimate commissions 53. The industry is thus caught in a paradox: as data collection becomes heavily restricted by privacy protocols, marketers are simultaneously held to higher standards of accountable, fraud-free performance measurement 37.
Infrastructure Adaptations for Viral Measurement
To adapt to the deprecation of client-side tracking cookies, the expansion of ITP, and the strict enforcement of Link Tracking Protection, product and growth teams are systematically migrating their measurement architecture to Server-Side Tracking (SST).
Vulnerabilities of Client-Side Tracking
Traditional client-side tracking relies on the end-user's browser to execute JavaScript code, capture interaction data, and send that data directly to third-party analytics platforms 5455. This method is highly vulnerable. Ad blockers, poor network connections, and browser-level privacy features actively target and block these third-party scripts from firing or retaining data in local storage 543940. As privacy regulations like GDPR and CCPA expand globally, relying on the user's browser environment to manage compliance and data routing has proven technically fragile and legally risky 5540.
Transition to Server-Side Attribution Architecture
Server-side tracking fundamentally alters the data flow topology to bypass browser-level restrictions. Instead of the user's browser sending data directly to third-party platforms, the browser communicates only with the company's proprietary backend server - establishing a secure, first-party context 525441. The proprietary server then processes, filters, and routes the necessary data to the ad networks and analytics platforms via Application Programming Interfaces (APIs), such as the Facebook Conversions API (CAPI) or Google's Enhanced Conversions 525441.
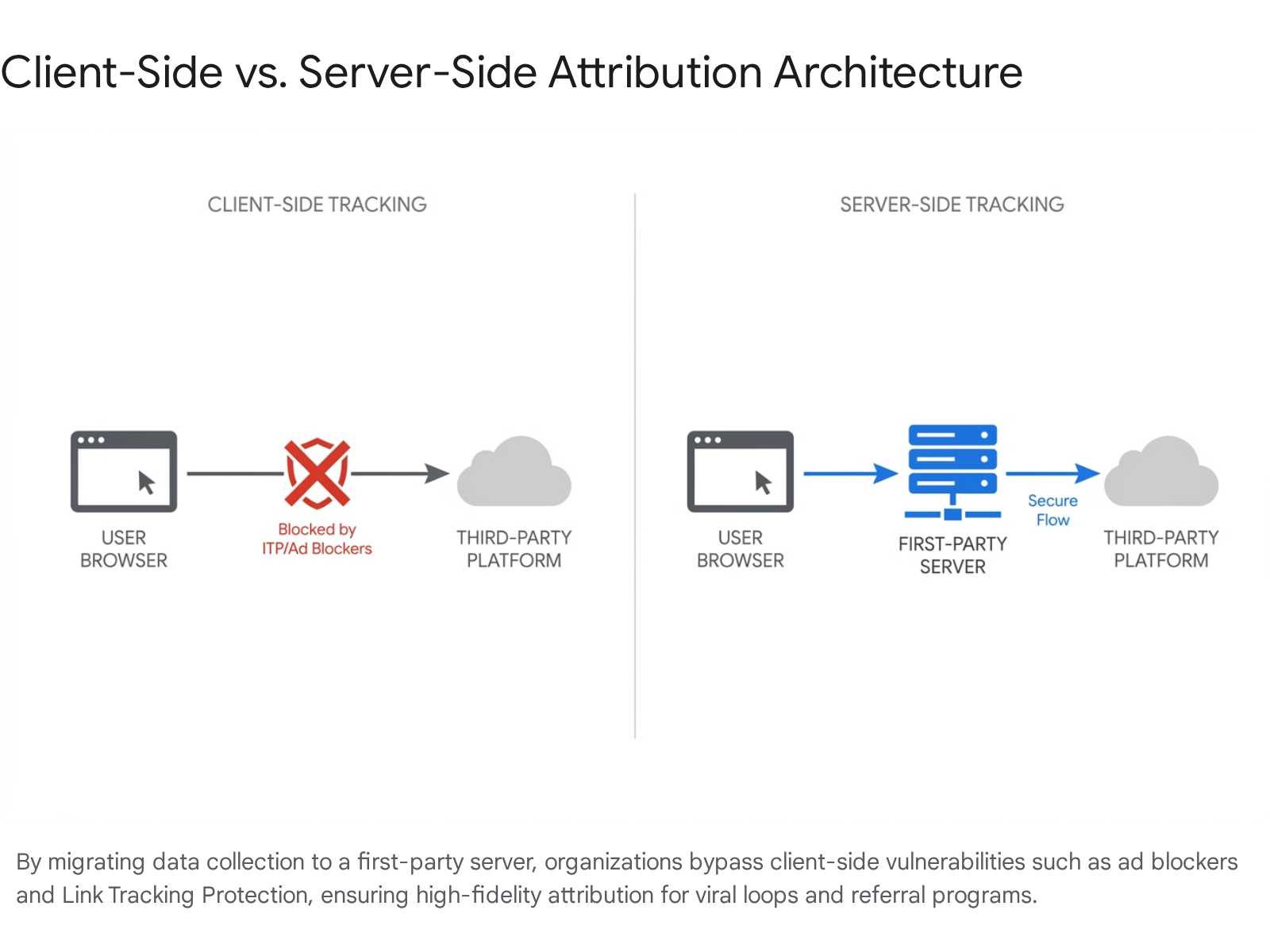
Because the initial data transmission occurs in a first-party context (between the user and the website they directly requested), it is generally exempt from the cross-site tracking restrictions that plague client-side pixels 3655. For example, if Safari attempts to hide a gclid from client-side JavaScript access, a server-side implementation can still capture the parameter directly from the initial HTTP request headers before the browser's restrictions apply 34.
| Architecture Type | Data Flow Path | Vulnerability Profile |
|---|---|---|
| Client-Side Tracking | Browser $\rightarrow$ Third-Party Analytics | High: Blocked by ITP, LTP, and Ad Blockers 54. |
| Server-Side Tracking | Browser $\rightarrow$ First-Party Server $\rightarrow$ API $\rightarrow$ Third-Party | Low: Bypasses browser restrictions via first-party context 41. |
This architecture provides superior data sovereignty, allowing companies to selectively filter out or enrich data before sending it to third parties, thereby enforcing data minimization principles and maintaining strict regulatory compliance 5455. By implementing hybrid tracking models that capture the initial user interaction client-side while processing the ultimate conversion server-side, businesses have reported recovering data attribution accuracy from degraded levels of 70% back up to 95 - 100% alignment with actual CRM revenue 5239.
Systematic Literature Reviews and Future Trajectories
The academic understanding of viral marketing continues to evolve in tandem with these technological shifts. A recent comprehensive systematic literature review (SLR) by Kaur, Kushwah, and Kumar (2025) analyzed 791 peer-reviewed papers to map the intellectual structure of the field 942.
Meta-Analyses of Viral Marketing Research
The meta-analysis indicates a fragmentation in how virality is studied, but successfully categorizes the existing knowledge base into five primary themes: the antecedents influencing customer viral decisions, the consequences of viral marketing, disseminating channel features, mutation and replication of viral messages, and viral measurement methodologies 942. Looking ahead, the bibliometric review identifies strategic focus areas shifting toward the cognitive processing of electronic word-of-mouth (eWOM), trust formation in peer-based digital interactions, and the intersection of viral propagation models with predictive artificial intelligence 43. As the mechanics of virality become increasingly algorithmic and server-dependent, future research must bridge the gap between complex measurement models and the authentic creation of value that naturally encourages sharing behavior 1.